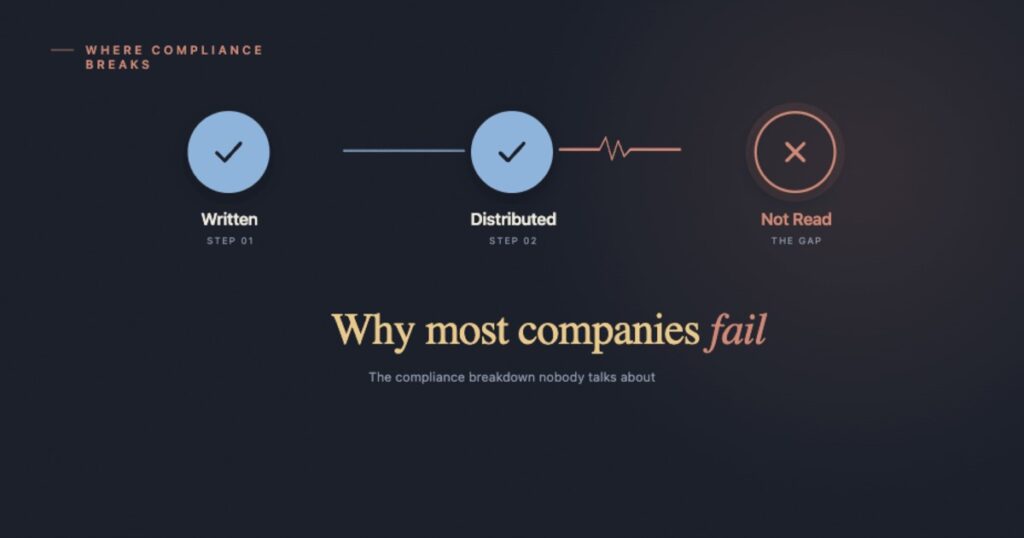
Every organisation has policies. Not every organisation has policies that employees actually read, understand, and follow.
That gap is where legal exposure lives. It is where regulatory audits become painful. And it is where a policy that took weeks to draft quietly fails to do its only job: guiding people’s behaviour.
Policy lifecycle management is the practice of treating a policy like a living process, not a one-time document. It covers everything from the first line of a draft to the moment an employee signs off and means it. Done well, it turns compliance from a box-ticking activity into something that genuinely reduces risk.
This guide walks through every stage of that journey, explains what goes wrong at each step, and shows you how to build a process your team can actually sustain.

What Is Policy Lifecycle Management?
Policy lifecycle management (PLM) is the structured, end-to-end process of creating, reviewing, approving, communicating, tracking, and versioning your organisation’s policies.
Here is the simplest way to think about it. A recipe has ingredients and steps. If you skip a step, the dish does not work, no matter how good the ingredients are. Policy management is the same. The policy itself is the ingredient. The lifecycle is the recipe. Miss a stage and the whole thing falls apart.
Most organisations do not have a broken policy. They have a broken lifecycle. We covered the structural reasons this happens in a separate article on why most companies fail at policy compliance. This guide focuses on the process side: what each stage of the lifecycle should look like.
Why This Matters More Than Most Teams Realise
Let us talk numbers for a moment.
According to Navex Global’s 2025 State of Risk and Compliance Report, 56 percent of risk and compliance professionals report that their organisation experienced at least one compliance issue in the past three years, and 36 percent experienced more than one.
The PwC 2025 Global Compliance Survey found that 72 percent of executives say increasing compliance complexity has negatively impacted their company’s profitability over the past three years.
Those numbers are not abstract. They represent real investigations, real fines, real reputational damage, and, in regulated industries like healthcare and financial services, real legal consequences.
What sits underneath most of those failures is not a lack of policy. It is a lack of policy management. Policies existed. Nobody could prove that employees knew about them, understood them, or agreed to follow them.
That is exactly what a proper lifecycle fixes.
The Seven Stages of the Policy Lifecycle
Stage 1: Initiation and Scoping
Every policy starts with a trigger: a new regulation, an audit gap, an incident that revealed unclear expectations, or a change in the business model. Initiation is about answering three questions before a single word is written.
Policies, simplified with AI-powered automation
Book a 20-minute demo to see how PolicyCentral.ai streamlines policy creation, distribution, and compliance across your enterprise.
Book a DemoWhy does this policy need to exist? A vague answer produces a vague policy. Tie it to a specific regulatory requirement or a documented operational risk.
Who owns this policy? Every policy needs a named individual or role responsible for its accuracy, review schedule, and eventual archiving. Without an owner, policies drift, contradict each other, and create confusion.
Who does this policy apply to? A policy for all employees looks very different from one for a specific team or role. Defining scope upfront prevents the “does this apply to me?” questions that slow down acknowledgement.
This stage is often skipped. Clarifying the problem, scope, owners, and success metrics before drafting begins lets you evaluate the policy’s effectiveness later and confirm alignment with compliance requirements.
Stage 2: Drafting
Now the writing begins, and this is where most policies quietly lose their audience. They are written for lawyers, not for the employees who have to follow them. Long sentences. Dense paragraphs. Undefined jargon. By paragraph three, the average employee has stopped reading.
Clear policy writing follows a few principles. Write at a reading level the whole workforce can handle. “You must not share customer data with third parties” beats “Employees are prohibited from engaging in the unauthorised disclosure of customer-related information to external entities.”
Use a consistent structure across every policy: purpose, scope, requirements, definitions, contact for questions. Predictable structure makes reading faster.
Reference related policies; do not duplicate them. Copy-pasting between policies creates version control nightmares.
Write for the person doing the job. A new employee on day one should be able to read the policy and know what is expected.
Version control starts here. Every draft should carry a version number, a date, and the name of the most recent editor. Built-in version control on the platform handles this automatically rather than relying on filename conventions.
Stage 3: Review and Approval
A draft becomes a policy only after the right people have reviewed it.
Subject matter input ensures the policy is practical. A cybersecurity policy written without IT input may demand things that are technically impossible. An expense policy written without finance may create approval chains nobody can follow. People follow policies they helped shape.
Legal and compliance review ensures the policy does not create liability or contradict existing obligations. In regulated industries, this is not optional.
Leadership approval gives the policy organisational authority and signals to employees that it matters.
Reviews need defined deadlines. Open-ended reviews drift like meetings without agendas. Set a window of five to ten business days per reviewer tier and build escalation for non-responders.
Approval must be documented. An email saying “looks good to me” is not adequate. A formal record showing who approved which version on what date, with reviewer comments captured along the way, is what makes evidence reportable when an audit comes calling.
Stage 4: Publication and Communication
A policy that has been approved but not communicated might as well not exist. Publication means more than uploading a PDF to an intranet folder no one visits.
Channel selection matters. A distributed field team needs a different approach than a corporate office team. Email, intranet posts, team meetings, and mobile notifications all have their place. The best approach combines more than one. Audience-targeted distribution ensures each policy reaches exactly the people it applies to, not the entire company.
Lead with the why. “We have updated our data handling policy because new privacy regulations require us to change how we collect and store customer information” gets more genuine attention than “Please review the attached updated policy.”
Summarise the key changes for policy updates so employees do not have to read the full document to figure out what changed. Respecting people’s time is a form of communication.
Make the policy easy to find. A centralised library with working search means any policy is locatable in under sixty seconds. Plain-language summaries for complex policies improve comprehension at the same time.
Stage 5: Training and Comprehension
Acknowledgement and comprehension are not the same thing. An employee clicking “I have read this policy” and an employee actually understanding what it requires of them are two very different outcomes. Training bridges that gap.
Role-specific training is more effective than generic. A data protection policy means different things to a customer service agent who handles personal data all day and an office manager who rarely touches it. Training that speaks to each person’s situation produces more genuine understanding.
Short and frequent beats long and rare. Four short sessions across the year produce more retention than one annual e-learning module. Spaced repetition works; annual policy dumps do not.
Test comprehension. Even three or four scenario-based questions after a policy module gives compliance teams useful data on whether the policy is being understood as intended. AI-generated summaries and FAQs reduce the upfront effort for employees too.
Stage 6: Acknowledgement and Attestation
This is the stage that creates your legal paper trail, and the one most organisations handle badly.
A proper acknowledgement is more than a checkbox. It is a documented record that a specific individual confirmed on a specific date that they had received, read, and understood a specific version of a specific policy. Every element matters.
Why version-specific acknowledgement matters. If an employee acknowledges version 1.2 of your code of conduct and an incident later occurs under version 1.4, you need to show what version they acknowledged and whether the relevant section had changed. Generic acknowledgements are legally weaker and operationally useless.
Automated reminders are not optional. Manual follow-up does not scale. Acknowledgement tracking with digital signatures handles reminders, escalation, and reporting end-to-end, with a clear path from automated nudge to manager notification to HR involvement.
Recurring acknowledgements keep compliance current — annual sign-offs for some policies, fresh sign-offs after every material update for others.
One thing to address directly: a high acknowledgement rate alone does not mean you are compliant. It means your distribution and reminder systems are working. Compliance is acknowledgement plus understanding plus behavioural change. Necessary, not sufficient.
Stage 7: Monitoring, Review, and Archiving
Policies do not stay relevant on their own. Regulations change, business processes change, technology changes. Policies that are not reviewed regularly become obstacles, either by demanding what is no longer possible or by failing to cover risks that now exist.
Set review cycles at the point of publication. Every policy needs a review date assigned the moment it goes live. Annual is a reasonable default; faster for fast-changing regulatory areas.
Use data to identify gaps. A real-time compliance dashboard lets you track incidents that may indicate policy gaps, alongside repeated questions to HR or compliance helpdesks. Repeat questions about the same topic usually mean the policy is unclear.
Archive outdated policies deliberately. When a policy is replaced, the old version is not deleted. It is formally marked as archived, removed from active circulation, and preserved for audit purposes. Employees should never accidentally follow an outdated procedure.
Archiving is not failure. It is governance working correctly.
Common Mistakes That Break the Lifecycle
Understanding the stages is useful. Understanding where organisations consistently fail is more useful.
Treating approval as the finish line. Many policy programs invest heavily in the drafting and approval process and then treat distribution as an afterthought. The policy is approved, emailed out, and considered done. This misses the point. A policy’s effectiveness is determined entirely by what happens after approval.
No named owner. Policies without owners get forgotten. They sit in a shared drive until they are discovered during an audit, at which point nobody can remember when they were last reviewed or whether they still reflect actual practice.
Acknowledgement without comprehension. The riskiest version of a compliance program is one that has excellent acknowledgement rates and no evidence that employees actually understand what they acknowledged. This creates false confidence while leaving the organisation exposed.
Inconsistent enforcement. If some employees are held to a policy and others are not, the policy loses its authority. Inconsistent enforcement is one of the fastest ways to destroy a compliance culture.
Manual processes at scale. Email-based policy distribution and spreadsheet-based acknowledgement tracking work for a team of ten. They collapse for a team of one hundred. As organisations grow, manual policy management creates gaps that are invisible until something goes wrong.
What Good Policy Lifecycle Management Looks Like in Practice
Let us make this concrete. Imagine a mid-sized financial services company with around three hundred employees across two locations. A regulator has announced changes to data handling requirements.
Without lifecycle management: Compliance sends an email with the updated policy attached. Some employees open it. Most do not. Six months later, during an audit, the team cannot produce evidence that employees were informed of the changes. The audit result is poor. The team scrambles to collect retroactive evidence of a process that was never properly run.
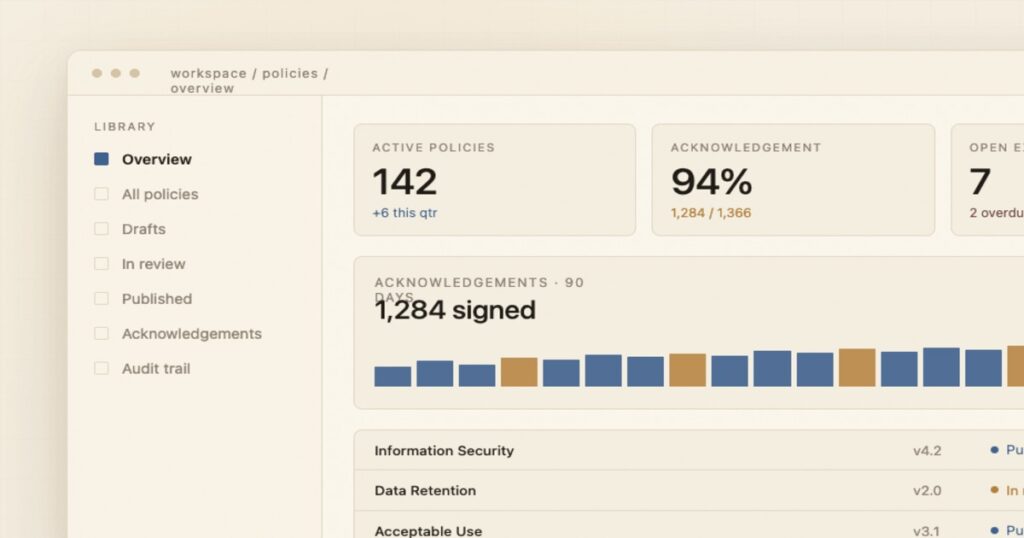
With lifecycle management: The team identifies the regulatory trigger, assigns a policy owner, and updates the policy with tracked changes. Legal reviews within five days. Leadership approves. The policy is published with a two-paragraph plain-English summary of what changed and why. Role-specific notifications go to the most affected employees. All three hundred receive an acknowledgement request tied to the specific version, with a fifteen-day deadline. Automated reminders fire at day seven and thirteen. Managers see a dashboard of their team’s status. By day fifteen, 94 percent have acknowledged. Non-responders are flagged for HR. A short quiz confirms comprehension for the highest-risk roles. Everything is logged with timestamps, versions, and individual records.
The audit result is very different in the second scenario.
The Role of Technology in Policy Lifecycle Management
Beyond a certain size, manual processes create too many gaps and too much administrative burden.
The data reflects this: Navex Global reports that 73 percent of compliance teams now use purpose-built technology specifically for policy and procedure management, second only to ethics and compliance training in tech adoption.
Good policy management software handles what humans cannot reliably do at scale. It maintains version control automatically. It tracks who has acknowledged which version and when. It sends reminders without anyone managing a spreadsheet. It generates audit-ready reports on demand. It flags review dates before they are missed. Our complete guide to policy management software covers the buyer-evaluation criteria in depth.
When evaluating tools, the questions that matter most:
- Does it tie acknowledgements to specific policy versions?
- Does it produce audit-ready reports with individual acknowledgements and timestamps?
- Does it support role-based distribution so employees only see what is relevant?
- Does it automate review reminders for policy owners?
- Does it integrate with your HR system so new joiners automatically receive their policies during onboarding?
Technology does not replace sound policy practice. It makes sound practice sustainable. PolicyCentral.ai’s policy management use case is built around exactly this principle.
A Note on Policy Culture
The most advanced lifecycle process will not fix a culture where policies are seen as bureaucratic obstacles. Culture is shaped by what leadership does, not what it says. When senior leaders are visibly subject to the same policies as everyone else, complete acknowledgements on time, and reference policies in decision-making, employees take them seriously. The opposite signal is just as clearly received.
A genuine policy culture also means treating acknowledgement as the start of a conversation about the policy, not the end of the compliance team’s responsibility. Feedback channels for unclear or impractical policies, and a willingness to act on that feedback, do more for compliance than another tool ever could.
Key Takeaways
Policy lifecycle management is not a documentation exercise. It is a risk management practice. A policy that employees have not seen cannot protect your organisation. A policy that employees have seen but do not understand is only marginally better. Only a policy that has been seen, understood, and acknowledged creates the foundation for genuine compliance.
The organisations that do this well do not just pass audits more easily. They have fewer incidents, clearer accountability, and a workforce that knows what is expected of it. That is worth considerably more than any individual policy document.
Frequently Asked Questions
What is the difference between policy acknowledgement and policy attestation?
Policy acknowledgement typically refers to an employee confirming they have received and read a policy. Attestation goes further, requiring the employee to confirm they have understood the policy and agree to comply with it. In regulated industries, attestation is often the minimum legal standard.
How often should policies be reviewed?
Annual review is the standard default for most policies. High-risk areas such as data protection, cybersecurity, and financial controls may require review every six months. Any policy in an area subject to frequent regulatory change should be reviewed whenever a relevant regulatory update occurs, not just on a fixed schedule.
What should be included in a policy acknowledgement record?
A complete acknowledgement record should include the employee’s name and identifier, the name and version number of the policy they acknowledged, the date and time of the acknowledgement, and confirmation of how acknowledgement was captured (digital signature, click-through, or other method).
What happens to policies when an employee leaves?
The acknowledgement records associated with a departing employee should be retained according to your organisation’s data retention policy and any applicable regulatory requirements. These records may be relevant in future disputes or audits. The policy owner should also review whether the departure affects any named roles or responsibilities within the policy itself.
Can a policy be enforced if an employee claims they never received it?
This is exactly why automated distribution with tracked acknowledgements matters. If your system shows that a notification was sent, a reminder was sent, and the employee either acknowledged or failed to acknowledge within the required window, you have a documented record. Without that record, enforcement becomes much harder and legal exposure increases.
What is the right team size to manage policy lifecycle processes?
There is no universal answer. The right resourcing depends on the number of active policies, the regulatory environment, the size of the workforce, and the level of automation in your process. Organisations with strong policy management software can handle significantly larger policy portfolios with smaller teams than those relying on manual processes.